Your data, your documents, always protected
Giving you the level of security that CFOs and CTOs expect.
At Procys, security is part of the platform from day one.
Every document, payment record, and e-invoice is protected with strong technical controls, clear processes, and transparent policies.
Sign up nowEvery document, payment record, and e-invoice is protected with strong technical controls, clear processes, and transparent policies.




Certifications and compliance
Procys meets strict EU and international standards so you can trust your e-invoicing data is secure.
ISO 27001-certified: Information is handled securely and kept separate for each customer.
.png)
GDPR-compliant: Personal and business data is handled with care.
.png)
NIS2-ready: These standards protect networks and information systems against cyber threats.
How we ensure secure document data extraction
Procys runs on Google Cloud Platform. Here’s why businesses trust Procys:
Outstanding protection
Encrypted storage and backups keep sensitive data secure
Data residency
E-invoices and financial data stay in Europe, meeting EU data residency requirements
Application security and
access control
Control who can see and act on your documents and e-invoices:

Secure access
Single sign-on and multi-factor authentication.

Customizable access controls
Role-based access for teams and users.

Audited actions
Complete logs for audits and compliance.
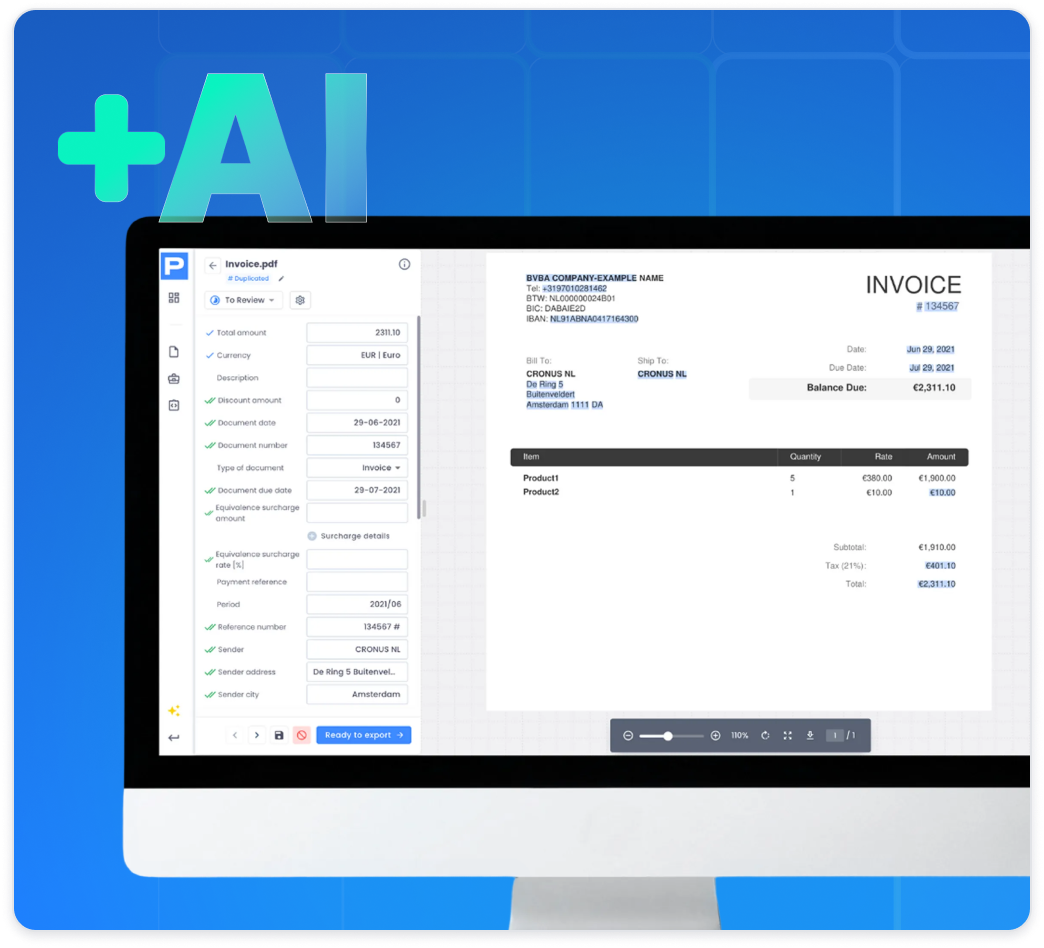
How we use
artificial intelligence
intelligence
Procys uses AI to process e-invoices and documents securely:
No selling of customer data or exposure to third-parties.
.png)
AI models are isolated per customer to reduce the risk of data leakage between users.
.png)
Full transparency on how your e-invoice data is processed.
Frequently asked questions
1. How does Procys ensure secure e-invoicing?
All e-invoices are fully encrypted. Role-based access, multi-factor authentication, and audit logs ensure only authorized users can see or process them.
2. How is e-procurement data secured?
Procys applies the same strict security controls to e-procurement documents as to e-invoices, including encryption, access control, and audit logging.
3. How does Procys protect electronic payment services and e-check processing?
All payment data is encrypted, access is restricted to authorized users, and every action is logged for compliance and audits.
4. Where is e-invoicing data stored?
All EU customer data, including e-invoices, is hosted on Google Cloud Platform (GCP), ensuring data residency compliance.
5. How does Procys handle AI processing of e-invoices?
AI models are isolated per customer and no data is sold. You can see exactly how your e-invoice data is processed and used.
6. Can Procys support Enterprise Risk Management (ERM)?
Yes. Audit logs, secure access, and controlled workflows help finance and IT teams monitor and mitigate risks.
7. Who can I contact for security questions or audits?
Our 24/7 email support is available for audits, compliance questions, and security reviews related to e-invoicing, documents, and payments. You can contact our team via support@procys.com.

Your security is
our priority
Procys builds security into every feature.
CTOs and CFOs across industries trust our AI-driven data extraction platform, knowing their e-invoices and documents are always protected with EU and international compliance built in, giving them true peace of mind.
